 One of the greatest nightmares of Internet of Things (IoT) supporters came to pass at the recent Black Hat confab in Las Vegas: security researchers presented a paper that identified a critical vulnerability in one of the wireless standards used for connectivity in multiple Internet of Things and smart home devices.
One of the greatest nightmares of Internet of Things (IoT) supporters came to pass at the recent Black Hat confab in Las Vegas: security researchers presented a paper that identified a critical vulnerability in one of the wireless standards used for connectivity in multiple Internet of Things and smart home devices.
The researchers from IT security firm Cognosec described how the ZigBee wireless mesh networking protocol used in many connected home devices leaves it open to attack through the method used to authenticate devices in its mesh network, despite the protocol’s use of high quality security.
The practical security analysis of every device assessed showed that the solutions are designed for easy setup and usage but lack configuration possibilities for security and perform a vulnerable device pairing procedure that allows external parties to sniff the exchanged network key.
— “ZigBee Exploited”, Tobias Zillner, Cognosec
It is important to understand that this is not a weakness in ZigBee as a protocol or any of the products that use it (from manufacturers including Samsung, Philips, Motorola, Texas Instruments and many more), but rather a weakness in the way that ZigBee is very often implemented that can be exploited. The discovery of this flaw is, without a doubt, not unexpected… to many it was inevitable: it is a direct result of the necessity for convenience of the consumer/end-user in the setup and maintenance of connected devices. This ease of use is paramount to the continued acceptance of the Internet of Things as most end-users desire hardware that simply works upon installation with little or no adjustment to function.
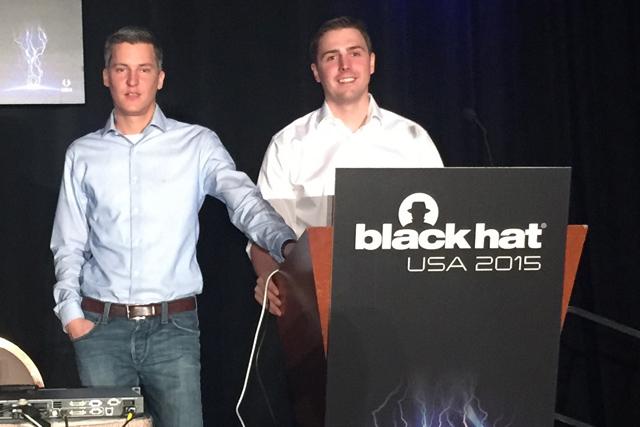
Image Credit: Engineering and Technology Magazine
Putting regulation on IoT devices and any potential failure will absolutely add to the cost of smart home devices and that may slow the adoption of such devices, but it is something that was always necessary — and now we have the proof to show why. This may hinder development of new devices by smaller companies and break-out startups (like Smart Things) might never enter the space but if my safety and security are at risk, a few dollars extra for every connected device is money well spent.

deez nuts
goooottteeeeeeeeeeeeeem!!!!!!!!!!!1
i fucked your mom last night